Protecting your personally identifiable information

In short:
- ‘Personally identifiable information’ refers to details that can be used to confirm who you are or how to find you.
- Keep your personally identifiable information private and regularly check your security settings to help protect yourself from bullying, scams and identity theft.
- If your personally identifiable information is misused or stolen, immediately update all your passphrases and report any suspicious activity in your accounts.
What is personally identifiable information?
Your personally identifiable information is any piece of information, or ‘data’, that can help to confirm who you are or how to find you. It may be information used on its own or in context with other information.
It can include everyday things that are specific to you, like your:
- full name
- parents’ names
- date of birth
- phone number/s
- home address
- location check-ins
- event RSVPs
- school
- email address
- photos
- usernames, passwords or passphrases
- Centrelink Customer Reference Number (CRN)
- bank account details.
Your credentials (also known as Evidence of Identity documents) could include:
- driver licence
- passport
- birth certificate
- proof of age card
- ImmiCard
- Australian visa or citizenship certificate
- Medicare card
- student ID.
Your identity information and credentials make up your legal identity.
Nearly every app, social media platform or website asks you for at least some personally identifiable information. But this data can be stolen or misused. That’s why it’s important to keep it as private and secure as possible. If you have to share it, make sure it’s only used by trusted services with your knowledge and consent.
Social media age restrictions
As of 10 December 2025, certain social media platforms are not allowed to let Australians under 16 have an account.
What you need to know:
- The age restrictions apply to Facebook, Instagram, Kick, Reddit, Snapchat, Threads, TikTok, Twitch, X and YouTube. See the latest list.
- Most standalone gaming and messaging apps, as well as many services that support health and education, are not affected by the new rules.
- You can still search for and see publicly available content that doesn’t require logging into an account.
- Under-16s won't get into trouble if they have an account on an age-restricted platform, but the platform could face fines of up to $49.5 million if it doesn't take reasonable steps to prevent underage accounts.
- If you do still have a social media account, it could be removed or deactivated at any time before you turn 16 - even if you've already passed an age check.
- No matter how old you are, if something goes wrong while you're on social media or anywhere else online, you should always reach out for support. eSafety's I need help page has advice and contacts.
Find out more at How do the social media age restrictions affect me?
Who wants my personally identifiable information?
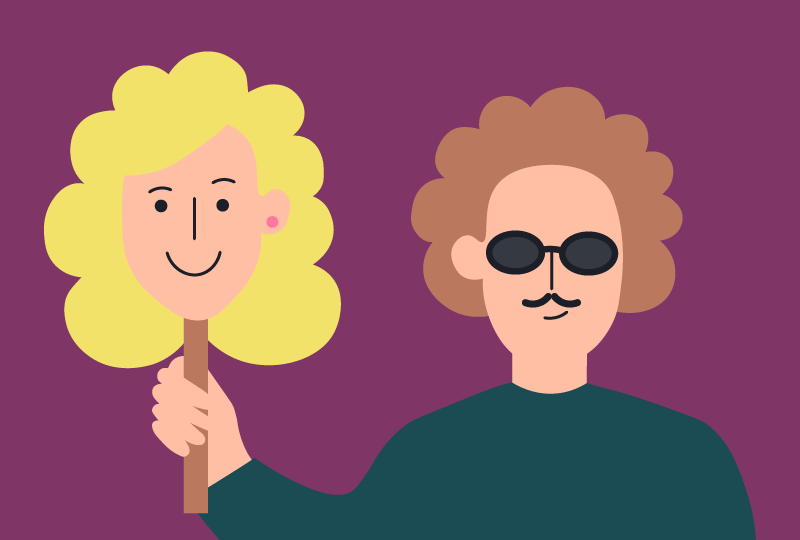
- Scammers and identity thieves. If scammers and identity thieves uncover your personally identifiable information, they can pretend to be you and create fake accounts in your name, and act in ways that could impact you now or in the future. This could include fraud like stealing money from your bank account or taking out a loan in your name.
- Bullies and doxers. There may be people on the internet who want to use your data for personal motives. A bully might use your email and password to pose as you and share mean or embarrassing content on your social media accounts, while a ‘doxer’ might share your street address and name with people who want to scare or harm you.
- Social media companies, games, apps and shopping sites. Many companies collect your data to make money through selling it to marketers or by targeting you with personalised ads. If the service is free, generally it’s your data that is being sold!
How can I keep my personally identifiable information secure?
Set up multi-factor authentication or a strong passphrase
Multi-factor authentication (also known as 2-step authentication) adds an extra layer of security to accessing your information that only you can manage. This means that when you log into an account with your password, you might be asked to do an extra step to confirm that it’s you – like enter a code from a text message or even face ID.
If you can’t set up multi-factor authentication, your next best option is to set up a passphrase – this is a password that is made up of four or more random words. Try thinking of a different passphrase for each of your accounts and don’t recycle parts of any old ones. A password manager app or your computer or phone can also help you create and remember complex passwords that are hard for others to guess or hack.
Never share your passwords or passphrases with anyone else. Almost 1 in 5 teenagers have shared the password to their social media accounts with a friend, family member, boyfriend or girlfriend. It may seem like a way of saying ‘I have nothing to hide’, but it’s never a good idea to let anyone else know your passwords – it increases your risk of cyberbullying and hacking of your personal information.
Learn more about multi-factor authentication and passphrases at cyber.gov.au/learn/passphrases.
Update and back up your devices
Hackers, scammers and cyber criminals can break into your devices if there are unpatched weaknesses in the system or apps. It’s important to update your devices with the latest software to make sure these security weaknesses are fixed. If you have antivirus installed on your devices, make sure to also check for regular updates from the software provider.
It’s also good to keep a digital copy of important information, including personally identifiable information. Saving backups of important files – like photos, documents and videos – to an external storage device or the cloud can help restore information if something goes wrong.
Find out more about updating your device and creating backups.
Connect to secure wi-fi networks
Scammers and cyber criminals have the chance to access your personally identifiable information through ‘Free’ wi-fi hotspots in public places, such as airports, cafes and libraries. When you need to access important accounts or send sensitive information, connect to a trusted internet connection, such as at home, at work or by using your own mobile data if it’s available.
Be aware of other threats like ransomware, phishing emails and texts where your personally identifiable information might be at risk of being shared or accessed by more people than just you.
You can check services like haveibeenpwned.com to find out whether a site or app you use has had a data breach (when your information that is meant to be secure has been revealed to others or stolen). If this has happened, change your passwords or passphrases straight away.
For more information about public wi-fi hotspots and other common cyber security threats, visit cyber.gov.au/learn/threats.
Report scams
Is an app, email or text asking you to input lots of personal information or provide your login details for any social media accounts? If so, it’s likely to be a scam.
Being alert to a scam message can help you protect yourself online. If you’re unsure whether the message you’ve received is a scam or not, go directly to a source you can trust (for example, a bank’s website). From here, you can check what details they might ask from you if they need to confirm any details about you or your account.
Make sure not to click on any links, open attachments or reply to the scam message – this might be a way for the scammer to trick you into sending your personally identifiable information. If something sounds too good to be true, it’s probably a scam.
For more information about scams, visit cyber.gov.au/learn/scams.
Check any websites or apps that ask for your personally identifiable information
Some websites and apps are built by scammers and are designed to collect people’s personally identifiable information, so they can hack your accounts or steal your money. If it looks dodgy, don’t hand over any personal information. Here are some quick tips for identifying dodgy sites and apps:
- Check that the URL for a website is the main URL you normally use to access that site.
- A padlock beside a site name in the address bar or a URL that starts with ‘https’ instead of ‘http’ can mean a site is more secure than other sites.
- Check that the branding is accurate – that it appears the same across all platforms, the logo is not blurred and the spelling is correct.
- Check your app store for reviews of apps before you download them. If there are lots of users and good reviews, it’s unlikely to be a scam. If there aren’t any reviews, do an online search – scams usually get identified fairly quickly and people often post online about them.
- Check out Scamwatch and Stay Smart Online.
Check your settings
The big social media sites and other apps that most people trust with their information offer privacy controls, so make sure you use them. Every once in a while, check your settings and see if you’re OK with how your data is being used or how much information you’re sharing with other people, including potential advertisers. If you’re not happy, change it up! For more info about privacy settings see The eSafety Guide.
On an iPhone you can go to Settings > Privacy to check which tracking and advertising options are active and which ones you would like to limit. For an Android phone, go to Settings > Privacy and find the Ads section to opt in or out of the ad preferences. Although this may not limit the amount of ads you see, it will make them less personally targeted, if that’s what you prefer.
Different apps and online platforms have their own tracking and advertising settings you can manage and change as well, such as Facebook, Instagram, TikTok, Twitter, Snapchat and YouTube. Check out The eSafety Guide for more information.
Be careful about who you add as a friend online
When you get a friend or follow request from someone you don’t know, check their profile. See if you have any mutual friends. If you’re feeling unsure, delete the request! Just like you’d find it weird if a stranger stopped you on the street, don’t let them follow your online profile. Take a look at our advice about unsafe or unwanted contact for more information.
What should I do if my personally identifiable information is misused or stolen?
Stay calm. First things first: if your data has been misused or stolen, understand that it’s not your fault. The person who used your information without your consent is the one who did the wrong thing.
Log yourself out of your accounts on all devices. This will log everyone out – including the person who’s using your information.
Change your passphrases on your accounts. Right after you log out of your accounts, log in on a safe device and update your passphrase to something new and secure.
Check your accounts for any suspicious activity. Check to see if anything has changed or seems out of place. Hackers and scammers may not take advantage of your personally identifiable information straight away. Keeping an eye out for suspicious transactions, emails or other forms of contact can help you understand if and how your information is being misused.
Screenshot and report online abuse. This is important if someone has created a fake account in your name, or a hacker has leaked your personally identifiable information (called ‘doxing’). The eSafety Guide has information about how to do this on different sites and apps. If a hacker has leaked your intimate images or videos, this is called image-based abuse and should be reported to eSafety straight away.
Report cybercrimes like identity theft or fraud to the Australian Cyber Security Centre (ACSC). If it was part of a scam, Scamwatch can also help you.
Get more support. If you’re really concerned about what’s happened or you’re feeling a little out of your depth, talk with a friend, family member or someone else you trust. You may feel like you should be able to handle it yourself but talking to someone can make it easier to decide what to do and deal with the impact. You can also seek help from Kids Helpline (for 5 to 25 year-olds) or another confidential counselling or support service.
Something happened to me
‘I shared my ID details with someone who scammed me online – where can I get help?’
Report cybercrimes such as identity theft or fraud to the Australian Cyber Security Centre (ACSC). If it was part of a scam, Scamwatch can also help you.
Talking with Kids Helpline (for 5 to 25 year-olds) or another confidential counselling or support service may make it easier to deal with the impact.
‘Someone has used my password to set up a fake social media account in my name – where can I get help?’
Collect evidence. This includes screenshots of the fake account profile and any false posts made in your name.
Log yourself out of all devices and reset your passwords immediately. Logging out will log everyone out too, including the person who has your account. Once you do this, you can log in on a trusted device and change your password.
Delete any embarrassing posts or hurtful messages. If the other person has shared anything pretending to be you, it’s a good idea to post an explanation about what’s happened.
Report it to the platform. They can take action against the hacker, including suspending or deleting their account.
Talking with Kids Helpline (for 5 to 25 year-olds) or another confidential counselling or support service may make it easier to deal with the impact.
‘Someone shared my home address online and now I don’t feel safe – where can I get help?’
Screenshot and report it to the service or platform. The eSafety Guide has information about how to do this on different sites and apps. If they don’t help you, report it to eSafety.
If you are in immediate danger, call the police on Triple Zero (000).
Talking with Kids Helpline (for 5 to 25 year-olds) or another confidential counselling or support service may make it easier to deal with the impact.
‘Someone hacked my account and shared an intimate photo and video of me online – where can I get help?’
Report it to eSafety. We can help to have the photo and video removed.
Last updated: 10/02/2026